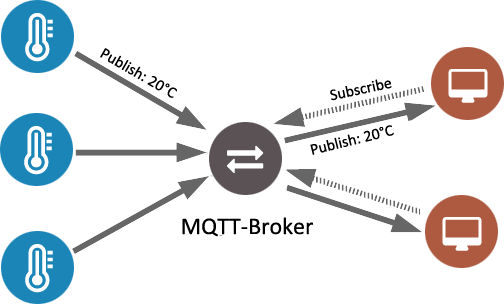
Recently I was working on an embedded Linux IoT device that communicated with cloud using MQTT protocol. The software in the device was divided into multiple applications that also required interprocess communication. We ended up using MQTT also for the local communication, and it turned out to be a good decision. Continue reading “Using local MQTT broker for cloud and interprocess communication”
Researchers produce first SHA-1 hash collision
Google security blog announced that they have been able to produce the first SHA-1 collision. That is, two different PDF-files with the same checksum. Finding the collision required nine quintillion (9,223,372,036,854,775,808) SHA-1 computations in total.
This may sound like a ridiculous amount but the research shows that, given the right resources, it is possible to break this hash algorithm. It is also noteworthy that this was not a brute-force attack which would still be impractical. In fact it was 100,000 times faster.
Now it is a good time to start using stronger hash algorithms such as SHA-256.
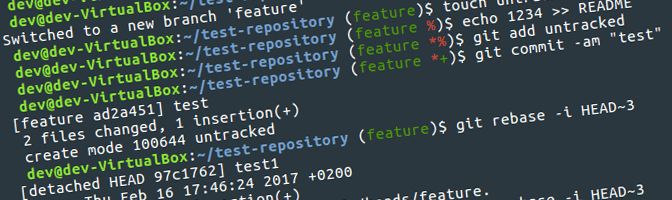
Improved git CLI with git-completion and git-prompt
Git-completion and git-prompt are scripts that provide versatile completion support as well as visualization of current branch and status when working from the command line. Even though I work with git daily I hadn’t bumped into these scripts until quite recently. They have proven to be very useful, so I decided to share this tip. Continue reading “Improved git CLI with git-completion and git-prompt”
My editor of choice for C/C++: QtCreator + FakeVim
Even though I work with C/C++ projects that are not related to Qt technology, QtCreator has become my main code editor. Here I explain some of the main reasons why I prefer it over other alternatives. Continue reading “My editor of choice for C/C++: QtCreator + FakeVim”
C++ tips for easier unit testing
A while back I read the Working Effectively with Legacy Code by Michael C. Feathers. The book focuses on strategies and approaches to get existing untested legacy code covered by unit tests.
The book also includes more than twenty dependency-breaking techniques that can be used for new code as well to make it easily testable in the first place. Here I have picked three of the techniques that I have personally found most useful.
- Interfaces to abstract implementation
- Extract and override call
- Expose static method
How to use TPM for encryptions
Trusted platform module (TPM) is a secure element that can be used to securely generate and store keys. It has many possible uses, one of which is encryption of sensitive data. This article describes how to use TPM and tpm-tools package on Linux environment to encrypt different types of data, how to encrypt filesystem partitions and how to bind the encryption with device state.
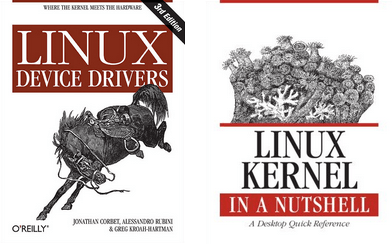
Free books for Linux kernel enthusiasts
In the true open-source spirit, the authors of some great Linux kernel books have decided to make these books freely available for everyone. They are good material for anyone interested in the Linux kernel, and also a good reference for professionals working with the kernel. At least I have personally found these books very useful.
The missing rootwait
Rootwait is a Linux kernel command line parameter that makes the kernel wait (indefinitely) for a root device to show up. This can be useful for devices that are detected asynchronously such as USB or MMC medias. This post, however, is not really about rootwait. Instead, it is about something that every programmer have and will encounter.
Continue reading “The missing rootwait”